Pentest report writing in 5 minutes (Defcamp 2018 talk)

- Article tags
Tired of writing pentest reports? Let’s automate this process and let you get back to hacking! Slides included.
Last Friday we had the pleasure to participate in Defcamp 2018 – the biggest security conference in Central Eastern Europe.
Besides having an exhibition booth there and talking to a lot of interesting people, Adrian Furtună, our founder &CEO, held a presentation about our newest feature: the Pentest Report Generator.
The idea is to decrease the time (and friction) spent with report writing and forget about formatting, executive summaries, introductions, and other details. This feature tries to cover as much as possible of this effort in order to leave the pentester focused on the interesting stuff.

The report generator is based on another new feature that we’ve added: Findings. This is a new view in the application which contains the aggregated results of all the scans from the current workspace. Having this aggregation, you can now select which findings you want to include in the report and press the button Generate Report.
You will obtain an editable report (.docx for Microsoft Word) that is well-formatted and ready to be shipped to your client.

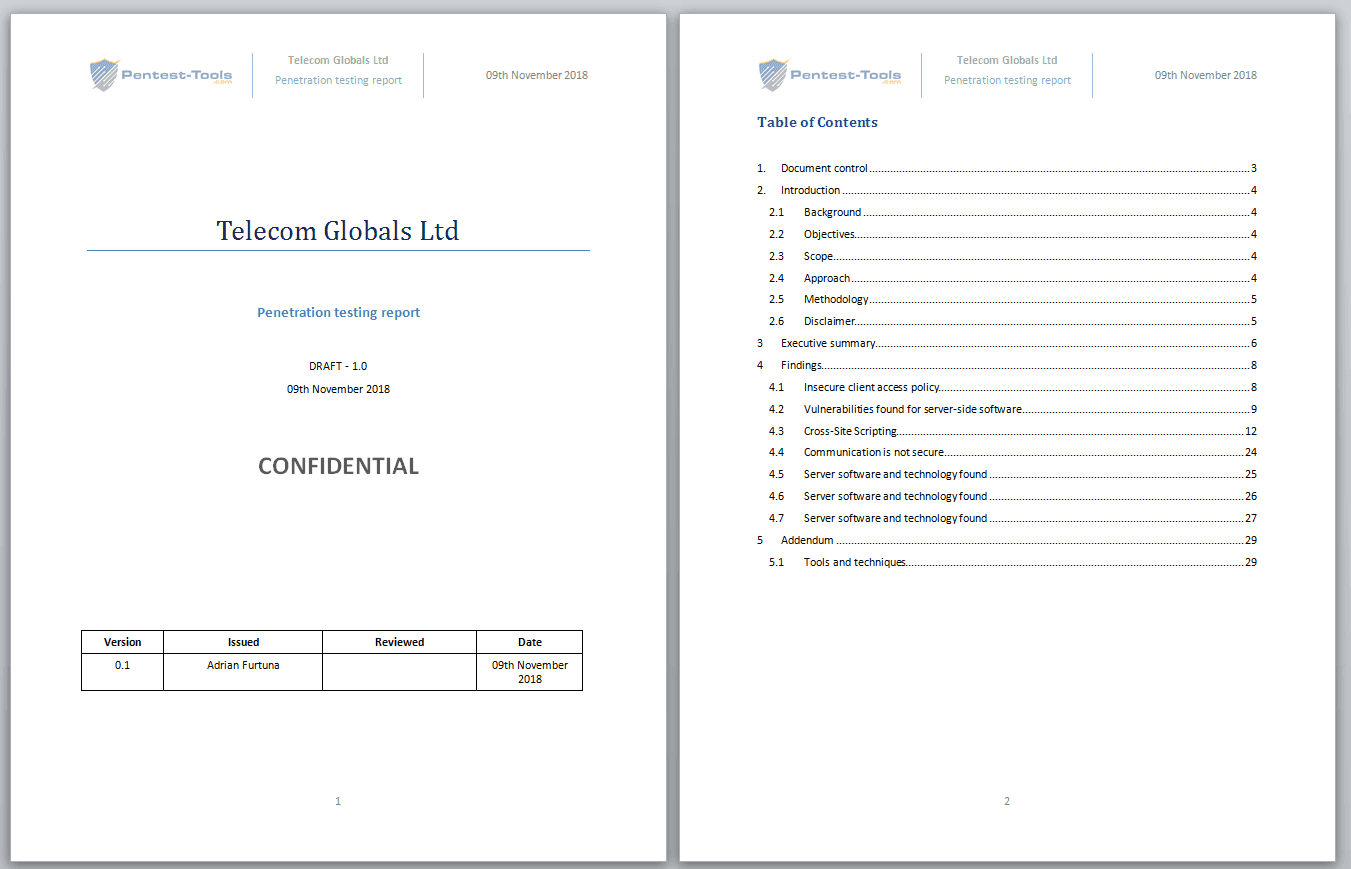
You also have the option to manually add findings obtained from outside the platform (other scanners or manually) so you are not bound to our scanners’ results.
When adding manual findings, you can take advantage of the Finding Templates feature, where you can have predefined findings with standard descriptions, risks, and recommendations. We will have a separate blog post dedicated to reporting writing and we will detail these features.
This video below shows how to generate editable pentest reports (.docx) from your findings in Pentest-Tools.com.
Update: Here is the full description of the Pentest Report Generation Tool.
Our awesome team
At the end of this short blog post, here is the Pentest-Tools.com team (at our Defcamp booth) which makes all the magic happen.

Here are the slides from our talk at Defcamp 2018. We will update this blog post with the video of the presentation when it will be available.
Update: You can watch the presentation here.
Feel free to try our report generation tool (currently the beta version) and send us feedback!
Thanks
We would like to thank Orange Fab Romania for facilitating our participation at Defcamp and also thanks to the Defcamp organizers who are doing a great job every year with this awesome conference!