Run laser-focused scans with these 5 platform updates

- Article tags
This month we roll out 5 fresh updates worth trying. Why?
Because we stack improvements so you can make little tweaks to your workflow that lead to massive time savings down the line.
1. Create custom headers (and use them with the URL Fuzzer)
2. Set up your own custom payload with the URL Fuzzer
3. Get email scan notifications about open ports
4. Find Subdomains – more search methods available!
5. Jira integration – info about targets & workspace added
Let’s unpack them!
1. Use your own HTTP headers with the URL Fuzzer
You can now set up your list of HTTP headers (Cookies or User-Agent) from your Pentest-Tools.com account.
To enable it, go to URL Fuzzer, insert your URL target, and specify a list of headers that are sent with each request included in the fuzzing process.
Use them to speed up how you uncover hidden files and directories in your web apps and how you check for common web vulnerabilities.
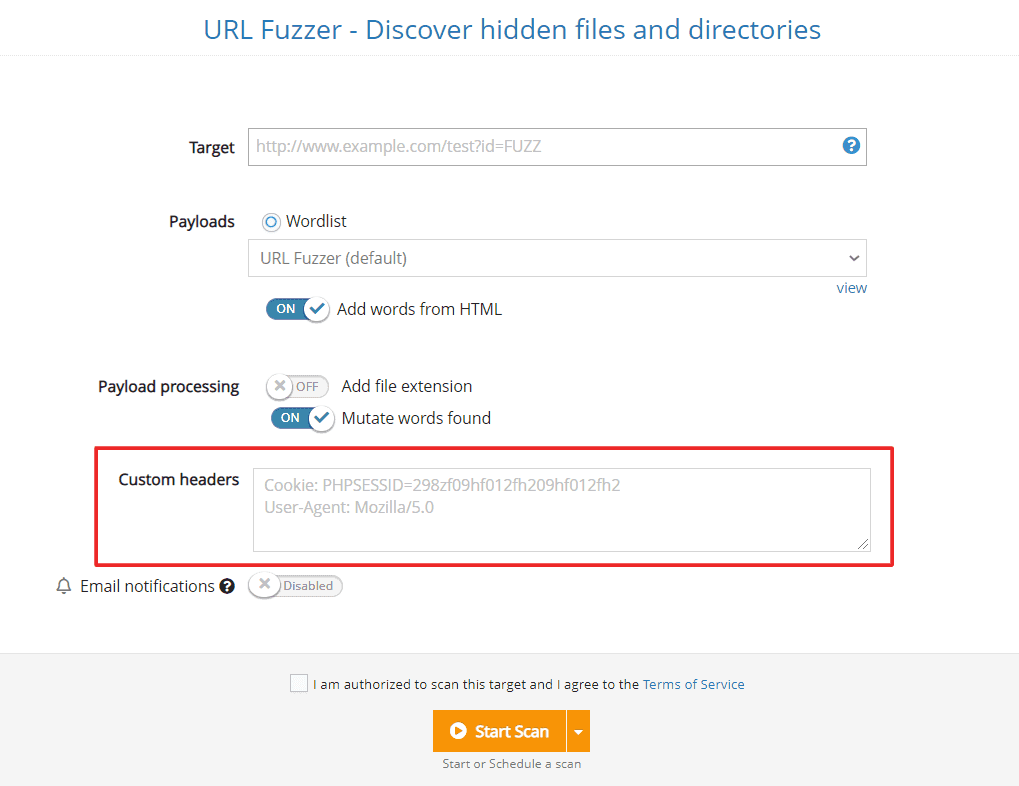
Set up custom headers
2. Add custom payloads in the URL Fuzzer to detect specific vulns.
Another improvement we’ve made to the URL Fuzzer is the option to add your payloads in custom locations using the “FUZZ” marker.
To do that, simply include them in the path of the URL or in the query string parameter.
Do NOT include them in the domain or subdomain if you want it to work.
Here’s an example:
http://example.com/dirs/FUZZ/index.php?id=3
3. Get email scan notifications about open ports
You can now set up email notifications for when Pentest-Tools.com finds open ports other than the ones you selected.
To use this feature, select one of our Tools, enable Notifications, and set the conditions about which open ports we should alert you.
When scan results match all your selected conditions, you’ll instantly be notified via email with the details.
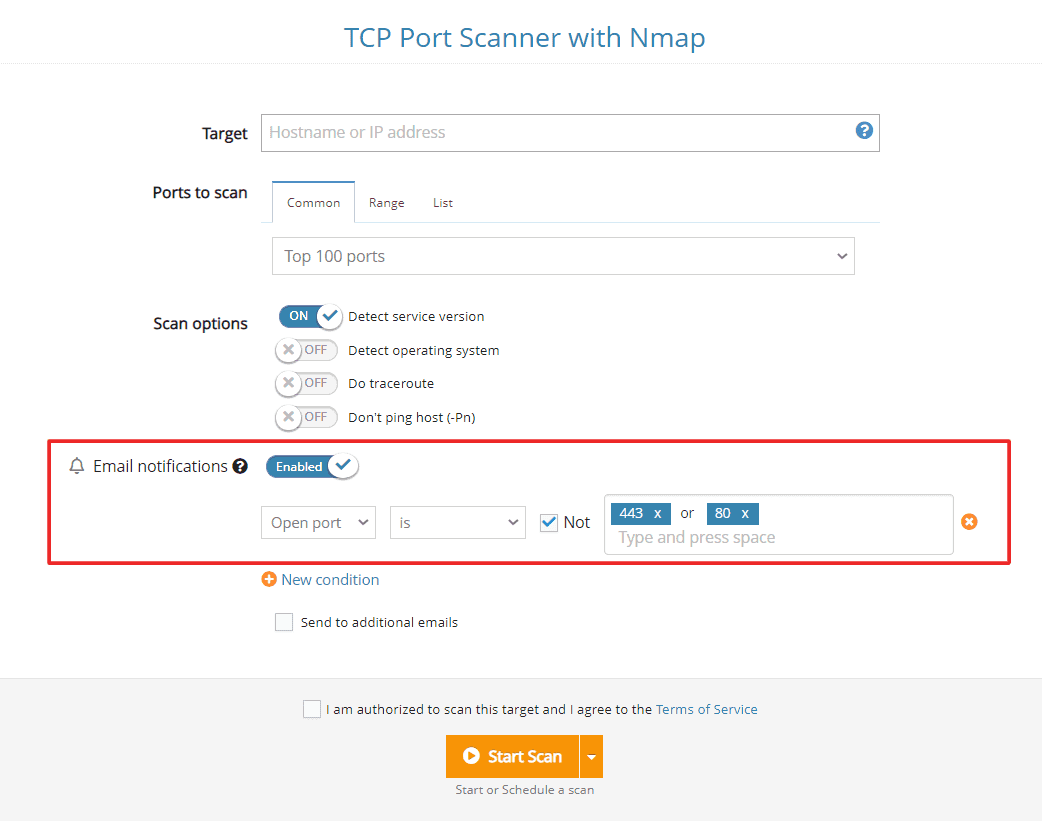
Set alerts for open ports
4. Find Subdomains now includes more data sources
We’ve enhanced the Find Subdomains tool with more search methods so you can get better results with Pentest-Tools.com.
Use them to gather essential information about your targets for your pentesting engagements.
5. Add Target and Workspace to Jira tickets
If you’re using the Jira integration to better prioritize the findings you discover using our platform, we have good news!
You can now add the target name and workspace to the tickets you create and automatically send them to Jira.
Use it to prioritize specific issues faster and better scale your work.
Quick reminder: Jira integration is available for Enterprise customers only.
Ready to take these updates for a spin?