Detect & exploit the latest CVEs + more automation updates

- Article tags
“Great and getting even better” is what we commit to with each monthly update we roll out on Pentest-Tools.com.
So here are 6 fresh updates we deployed to make your security testing flow a lot easier, more flexible, and more efficient:
Detect 4 new, high-risk CVEs with the Network Scanner
Exploit 3 critical CVEs with Sniper Automatic Exploiterin <2 minutes
Control the requests/seconds limit in the Website Scanner
Automatically validated Website Scanner findings get a Confirmed tag
Clone pentest robots on Pentest-Tools.com
Manually reset your Pentest-Tools.com API key
Let’s dive into specifics!
1. Detect 4 widespread CVEs with the Network Scanner
Our vulnerability research team worked around the clock to embed new detection modules for the latest high-impact vulnerabilities.
Run our Network Vulnerability Scanner against your targets and check for:
the critical VMware RCE vulnerability in the vCenter server – CVE-2021-21985
entry points for the Microsoft Exchange Server RCE (ProxyOracle) – CVE-2021-31195
the SSRF vulnerability in VMware’s vRealize Operations Manager API – CVE-2021-21975
unauthenticated events in the Modern Events Calendar Lite WordPress plugin – CVE-2021-24146
Use the Full Scan option from the Network Vulnerability Scanner with OpenVAS and get a ready-to-use report with detailed findings.
2. Automatically exploit & confirm 3 critical CVEs with Sniper
If you haven’t tried it yet, take this chance to see how Sniper Automatic Exploiter validates, exploits, and does post-exploitation in under 2 minutes for the most recent critical vulns.
Automatically run a full exploitation sequence on your targets and get validation for:
the RCE vulnerability in VMware’s vCenter servers – CVE-2021-21972
the OGNL injection RCE in Atlassian’s Confluence servers – CVE-2021-26084
the unauthenticated OMIGOD RCE vulnerability in multiple Azure Linux machines CVE-2021-38647, among a dozen other widespread security flaws.
3. Limit the number of requests/second with the Website Scanner
You now have the option to control the maximum number of requests per second you make with the Website Scanner.
Go to Website Vulnerability Scanner, add your URL target, select Engine options, and choose Limits. From there, you can set a maximum of 10.000 requests/second.
Here’s what it looks like:

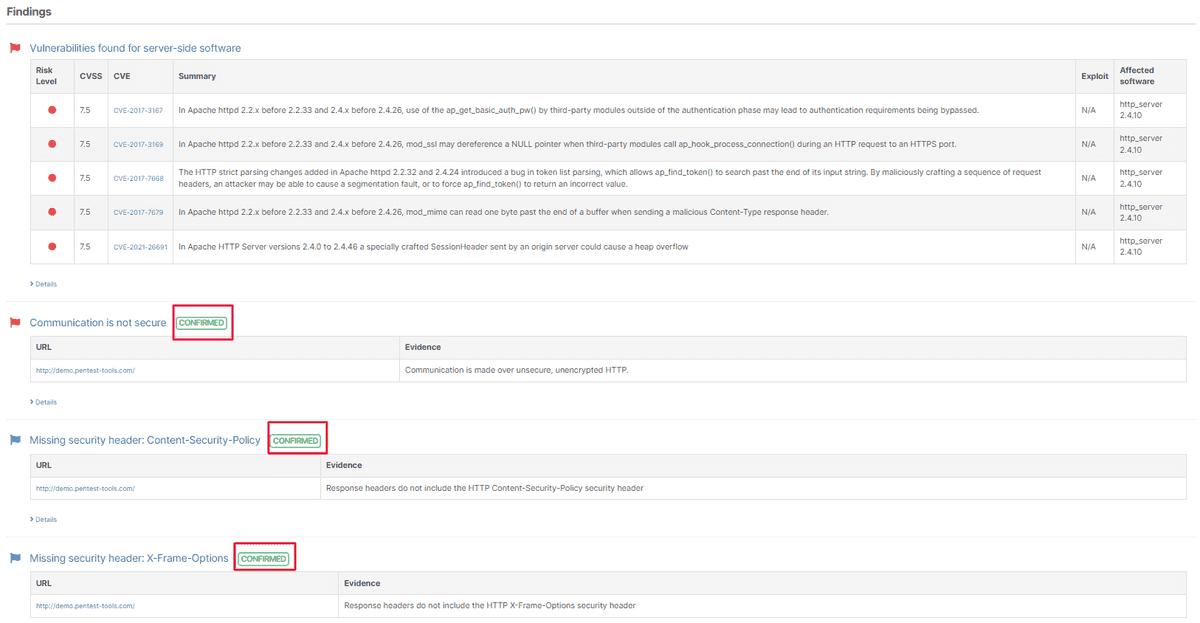
4. Automatically validated Website Scanner findings get a Confirmed tag
When you scan your targets with our proprietary Website Scanner, the discovered findings are automatically validated and get a specific tag.
Each finding is marked as Confirmed so you can easily select the interesting ones to include in the final pentest report.
Check it out:
5. Clone a predefined or a custom pentest robot
If you’re a heavy user of our pentest robots automation feature, you can now clone a predefined pentest robot or any of the robots you’ve already built.
Go to your pentest robot, click on the Clone button from the Actions tab, and use it in your engagements as you need – edit it, improve it or share it with your team.

6. Manually reset the API key authentication on your account
From your Pentest-Tools.com account, you can now reset your API key manually.
To do this, go to My Account, select Plan details, and click on the Reset API key button.
Before you go
We added 6 new auto-exploitation and detection modules in Sniper and our Network Scanner in the last month alone and the pace is picking up.
Do you want to find out when we launch new ones without waiting for the monthly platform updates? Get an email notification the moment new CVEs get integrated into Pentest-Tools.com.