Joomla Scanner
Technical details
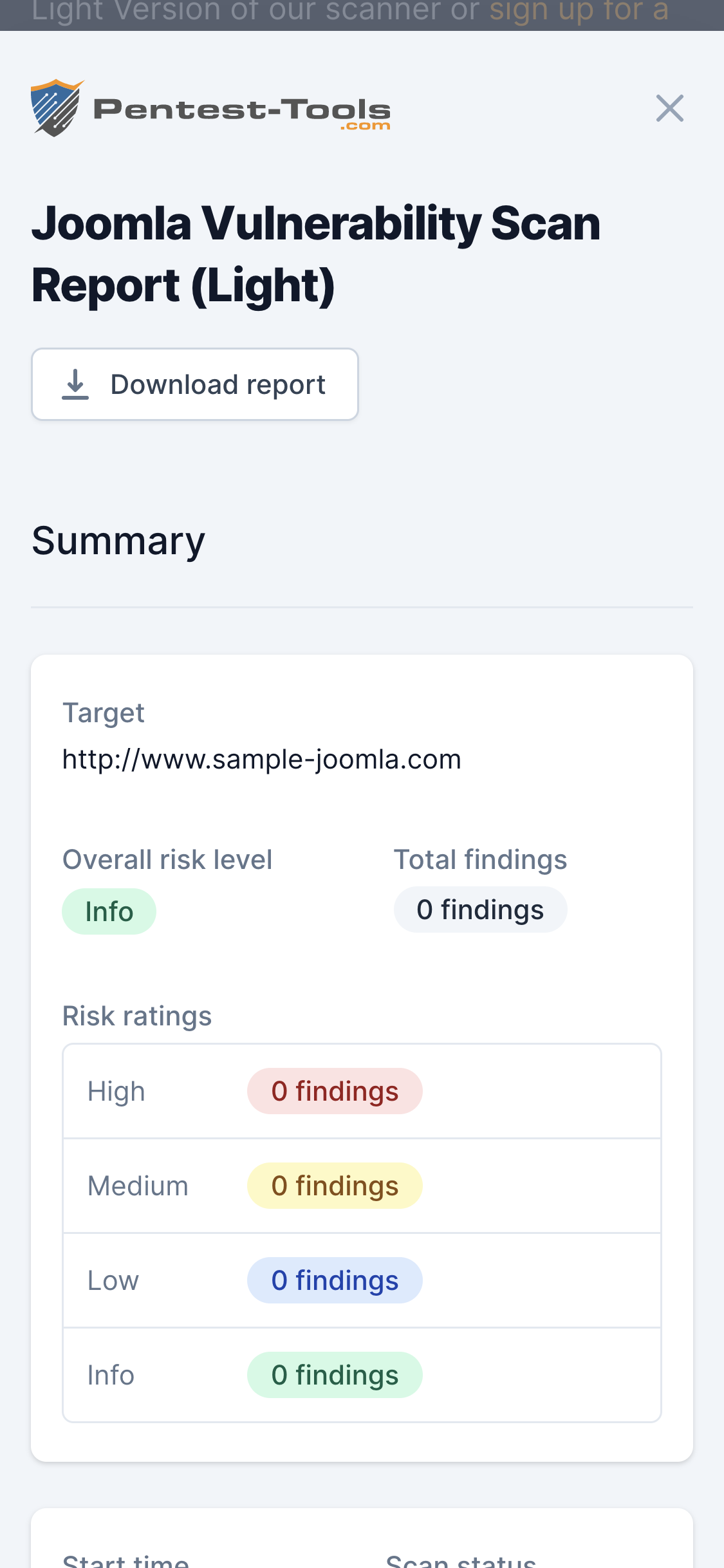
The scanner attempts to identify security weaknesses in the target Joomla website (core, components, modules, and templates).
It performs a remote scan without authentication, using a black-box methodology. It simulates an external attacker who tries to penetrate the target Joomla website.
The Joomla Vulnerability Scanner performs the following operations to assess the security of the target website:
- Detect the installed Joomla version
- Show vulnerabilities impacting the identified Joomla version
- Enumerate installed components and their versions
- Show vulnerabilities for the known components
- Enumerate the installed modules and their versions
- Show vulnerabilities for the identified modules
- Enumerate the installed templates and their versions
- Show vulnerabilities for the identified templates
Our scanner uses the well-known JoomlaVS JoomlaVS scanning tool engine.
Parameters
| Parameter | Description |
|---|---|
| Target URL | This is the URL of the Joomla website that will be scanned. All URLs must start with http or https. Don't forget to specify the complete path to the base directory of the Joomla installation. e.g http://targetjoomla.com/cms/. |
How it works
The scanner connects to the Joomla website target and retrieves information from the HTML pages to fingerprint the Joomla version.
The enumeration of components, modules, and templates is done by checking multiple known names.
The tool extracts the vulnerability information from a frequently updated database and includes them in the final report with references for vulnerability details.