Resources
Changelog
These are the latest updates we've made to our platform. If you have any questions about any of the updates you see below, please feel free to contact us!
Filter by
March 2026 Changes
New API endpoints for scan tests
OWASP Top 10 2025 classification in findings
Exploit for Remote Code Execution in Hikvision IP camera/NVR (CVE-2021-36260)
Exploit for Remote Code Execution in SolarView Compact (CVE-2022-29303)
Tests performed by a scan are now visible in results
Exploit for Remote Code Execution in MeteoBridge (CVE-2025-4008)
Exploit for Remote Code Execution in HPE OneView (CVE-2025-37164)
Plug and play with our new MCP server
Refreshed product documentation
February 2026 Changes
Pentest-Tools.com is ISO/IEC 27001:2022 certified
Detection & exploit validation for Ivanti EPMM RCE (CVE-2026-1281)
Authentication Bypass in GNU Inetutils Telnetd (CVE-2026-24061)
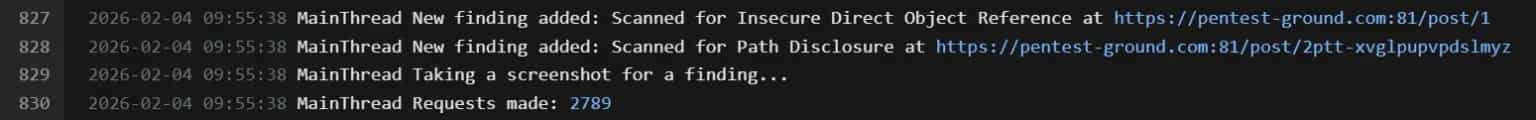
Deeper visibility into findings, directly in scan logs
January 2026 Changes
Allow filtering /scans API requests by tool
Exploit for WordPress SMTP Plugin account takeover (CVE-2025-11833)
December 2025 Changes
The Network Scanner is ready to detect CVE-2025-14847 - MongoBleed
You helped us make 2025 our most accurate year yet!
Exclusive exploit for React2Shell (CVE-2025-55182)
Exploit for CVE-2025-64446 & CVE-2025-58034 (Fortinet FortiWeb)
November 2025 Changes
Findings page is now taking port into account for grouping
Exploitation for CVE-2020-36847 (Remote Code Execution in Wordpress Simple File List plugin)
RCE
CVE
SQLi detectors uses more payloads in all custom cookies and has reduced false positives
Detection & exploitation for the React Native Community CLI development server RCE (CVE-2025-11953)
RCE
CVE
Detection for CVE-2025-55315 (HTTP Request Smuggling in ASP.NET Core)
Detection & exploitation for the Oracle RCE (CVE-2025-61882)
RCE
CVE
Added CL.0 request smuggling detection in our HTTP desync attacks active detector
October 2025 Changes
Download multiple reports at once
Exclusive exploit for Magento SessionReaper (CVE-2025-54236)
NEW: Vanta integration just got an upgrade!
Launch internal scans directly in Azure
September 2025 Changes
NEW: Burp Suite extension for pentesters
August 2025 Changes
Prioritize more accurately with EPSS scoring
Manage findings with more granularity
Import & track assets at scale
July 2025 Changes
Download scan group results directly from Reports
June 2025 Changes
Filter scan results by time with the API integration
Cut through the noise with ML-powered false positive filtering
NEW: Pentest-Tools.com x Nucleus Security for smoother findings management
Get more context with enriched JSON reports
May 2025 Changes
Identify mass assignment vulns with API scans
April 2025 Changes
Automate report generation with our new Reports API
Get richer findings with the Website Scanner
Start Pentest Robot scans directly from the New Scan flow
Prove real-world risk with these 3 new exploits
March 2025 Changes
Detect CVE-2025-29927, the vulnerability in Next.js middleware, fast and effectively
Edit scheduled scan notifications without starting over
Much easier tracking for pentest robot scan results
February 2025 Changes
Brute-force battle: we tested Hydra vs our Password Auditor against 26 web apps!
Tool: Password AuditorAnalyze findings faster with even more refreshed results
Tools: SQLi Exploiter | Web Application Firewall Detector | ICMP Ping | Whois Lookup | Joomla Scanner | Subdomain TakeoverZero in on critical web app flaws – lightning fast
January 2025 Changes
Make sure your scheduled scans are on track
Easier (custom) scan flows with Pentest Robots
December 2024 Changes
Check real-time results with People Hunter
Fresh scan results for your toolkit
November 2024 Changes
Monitor targets with scheduled scans in Free!
October 2024 Changes
NEW: Import your AWS targets with ease
Continuous monitoring made (even) easier
September 2024 Changes
Fresh look, enhanced Reports
Clone multiple Findings at once for faster edits








.png&w=1536&q=100)








.png&w=1536&q=100)


















![[New in free] Monitor your targets for new vulnerabilities with Pentest-Tools.com](/_vercel/image?url=https:%2F%2Fcontent.pentest-tools.com%2Fassets%2Fcontent%2Fmonitor---free.png&w=1536&q=100)






.png&w=1536&q=50)

.png&w=1536&q=50)