Domain Finder
Technical details
Domain names are Internet resources assigned to various companies around the world. A company can own multiple domain names which can be used for various purposes of the business (e.g. for the main website, for clients portal, for supplier applications, etc.)
Finding all the domain names owned by a company is an important step in the information gathering phase of a penetration test or during bug bounty activities. This is because these associated domains could expose resources of the company which are less secure than the ones sitting on the main domain.
For example, some of the associated domains for facebook.com are:
- facebook.net
- fbcdn.net
- fb.com
- messenger.com
- fbsbx.com
As a result, exploring the attack surface from the additional domains could be a fruitful path during pentesting or bug bounty.
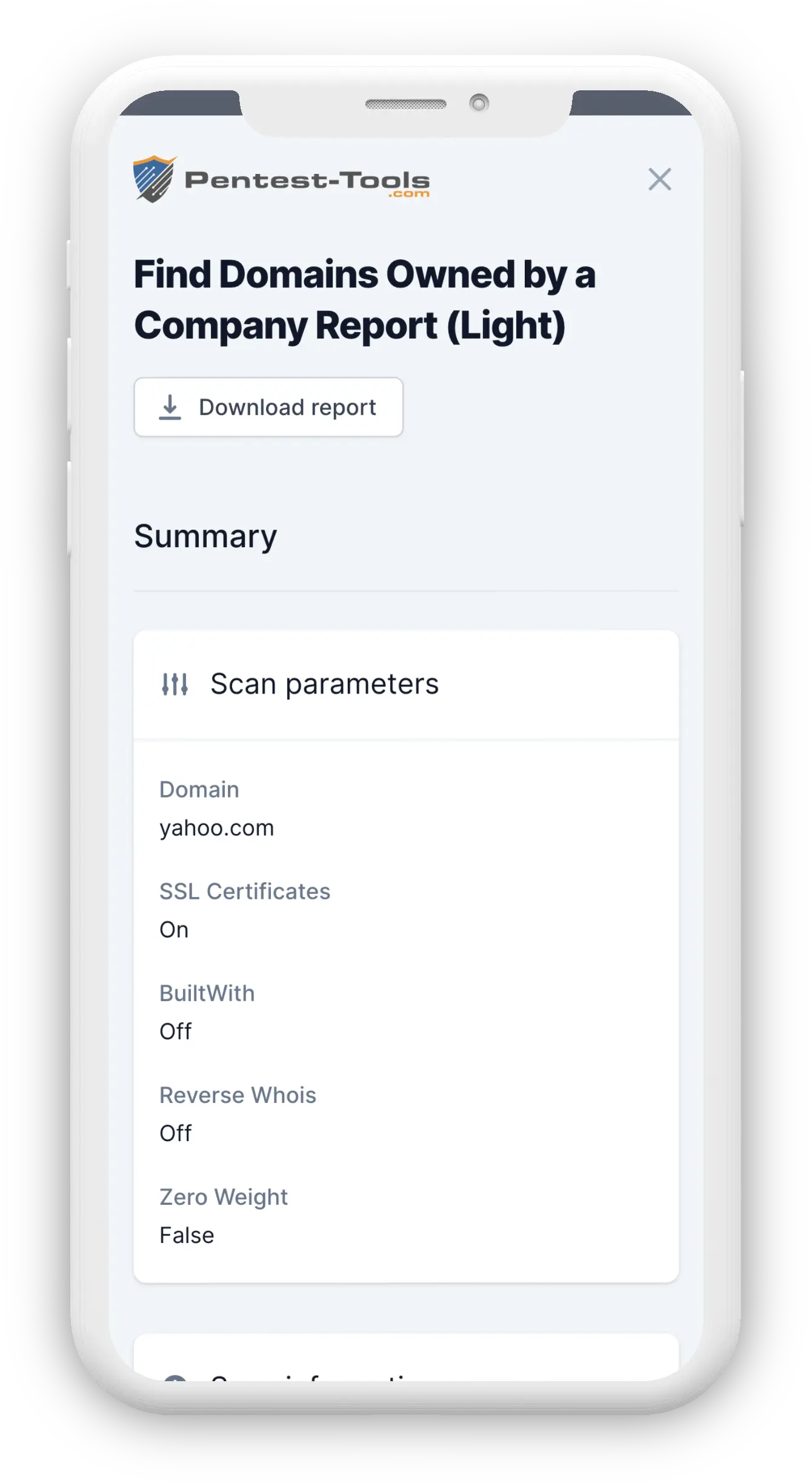
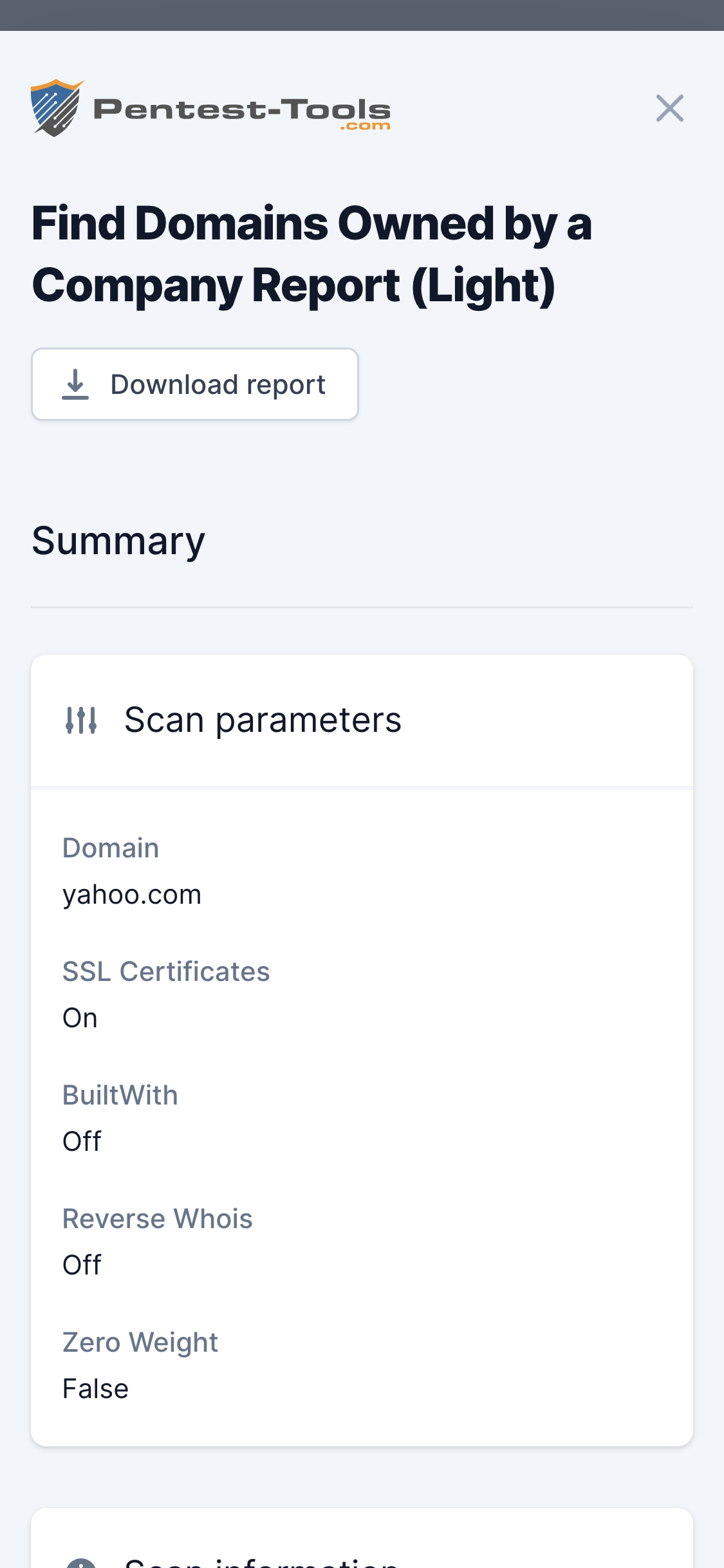
Parameters
| Parameter | Description |
|---|---|
| Domain name | Is the target domain name (e.g oracle.com, yahoo.com etc.) that will be searched for associated domains |
| SSL Certificates | Searches Certificate Transparency Logs for certificates having the target domain as alt name |
| BuiltWith | Searches BuiltWith relationships (e.g. Google Analytics Tags) for potentially related domains |
| Reverse Whois | Finds the company and contact email of the target domain with a Whois lookup and then does a reverse lookup on them |
| Minimum weight | The certainty (or the weight) that a domain should have in order to remain in the final list of results |
How it works
The tool assigns a certain weight to each result to validate its correctness. Validation uses these factors to determine accuracy:
- The organization name found in the SSL certificate, as well and the number of certificates linking the two compared domains
- The number of BuiltWith relationships and duration of those relationships
- Matching Whois records (companies, emails)
- Domain name similarity (e.g.
amazon.de/amazon.com) - Redirect history: checks if the found domain redirects to the base domain or vice versa (e.g.
gmail.com->mail.google.com)