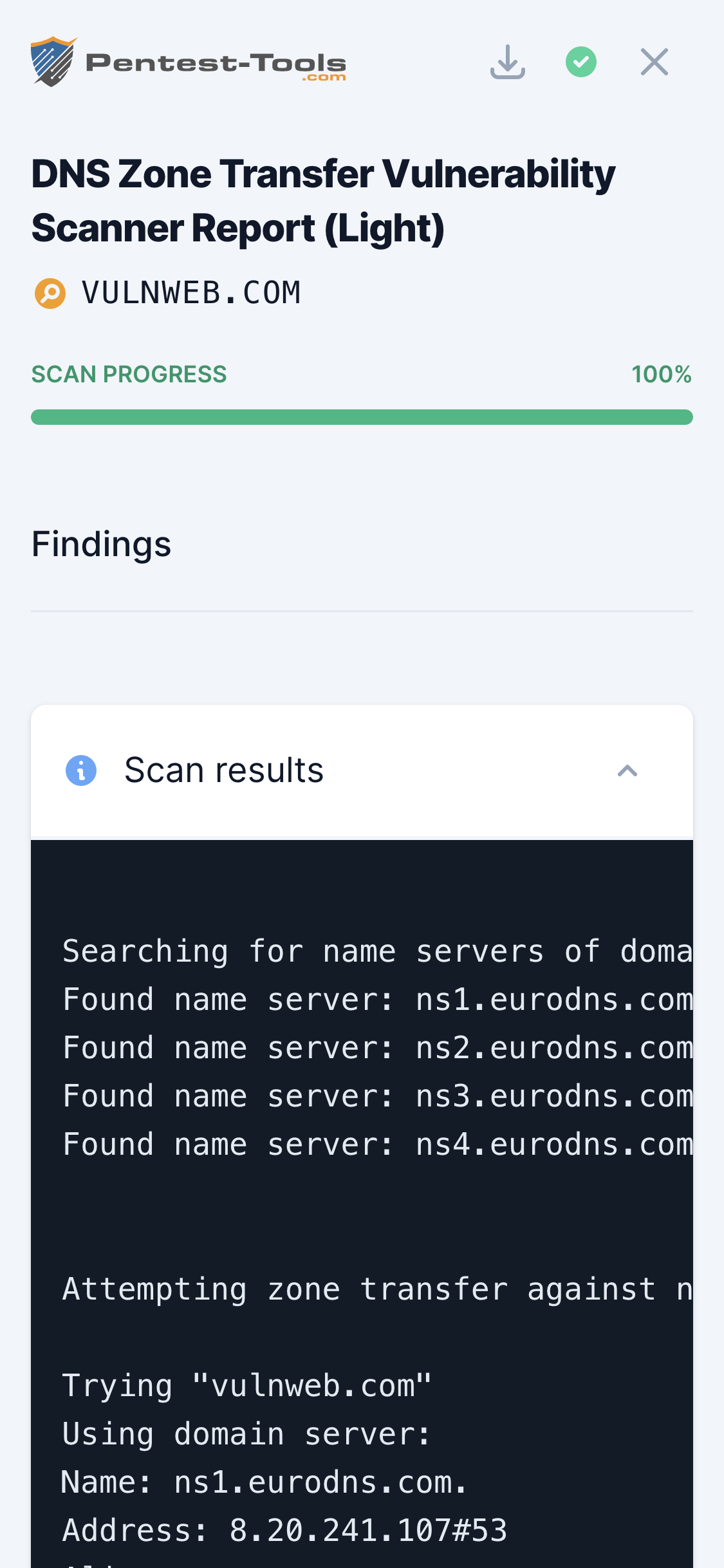
DNS Server Scanner
Technical details
DNS servers shouldn't allow zone transfers towards any IP address from the Internet.
Zone files contain complete information about domain names, subdomains, and IP addresses configured on the target name server. It is relevant to find this information because it helps increase your attack surface and better understand the internal structure of the target company (e.g., detect test servers, development servers, hidden domains, internal IP addresses, etc.)
Information gathered from zone files can help attackers implement various attacks against the target company, like targeting test or development servers that are less secure.
Parameters
| Parameter | Description |
|---|---|
| Target domain name | This is the base domain name for which you want to try zone transfer. |
How it works
The tool starts by discovering all the name servers associated with your target domain. Then, to each name server, it sends a Zone Transfer (AXFR) DNS request and checks if it is successful or not. In case of success, the entire zone file is displayed.