Website scanner introduction

Latest scanner updates
False positives don’t just waste time - they erode trust, delay remediation, and bury real issues under a pile of noise.
That’s why we’ve built and integrated the Machine Learning classifier - a purpose-trained machine learning model - directly into our Website Scanner and URL Fuzzer.
Instead of relying on brittle RegEx logic, the ML Classifier analyzes every HTML response during a scan and automatically sorts it into one of four smart categories:
📌 HIT – High-value targets like login pages, exposed secrets, and backups
📌 MISS – Confirmed dead ends, even when status codes are misleading
📌 PARTIAL HIT – Ambiguous but interesting results (like firewall pages or redirects)
📌 INCONCLUSIVE – Requires browser-based rendering for confirmation
This means you can quickly focus on what matters, reduce triage time, and get clearer, cleaner results.
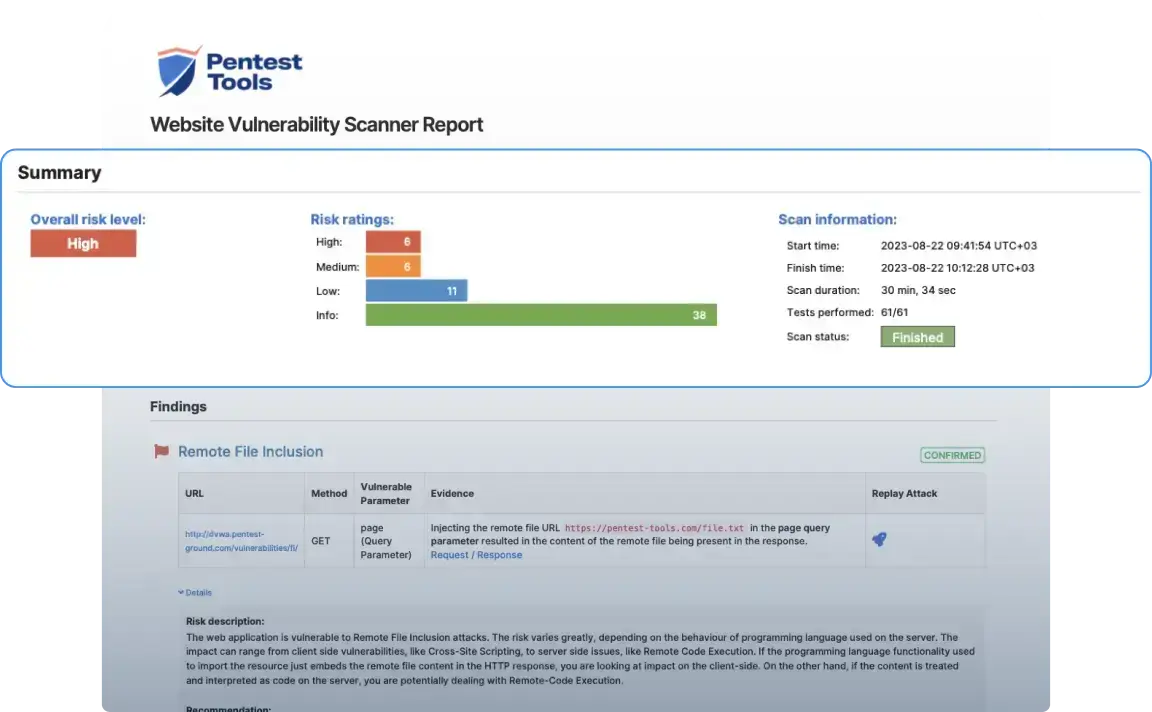
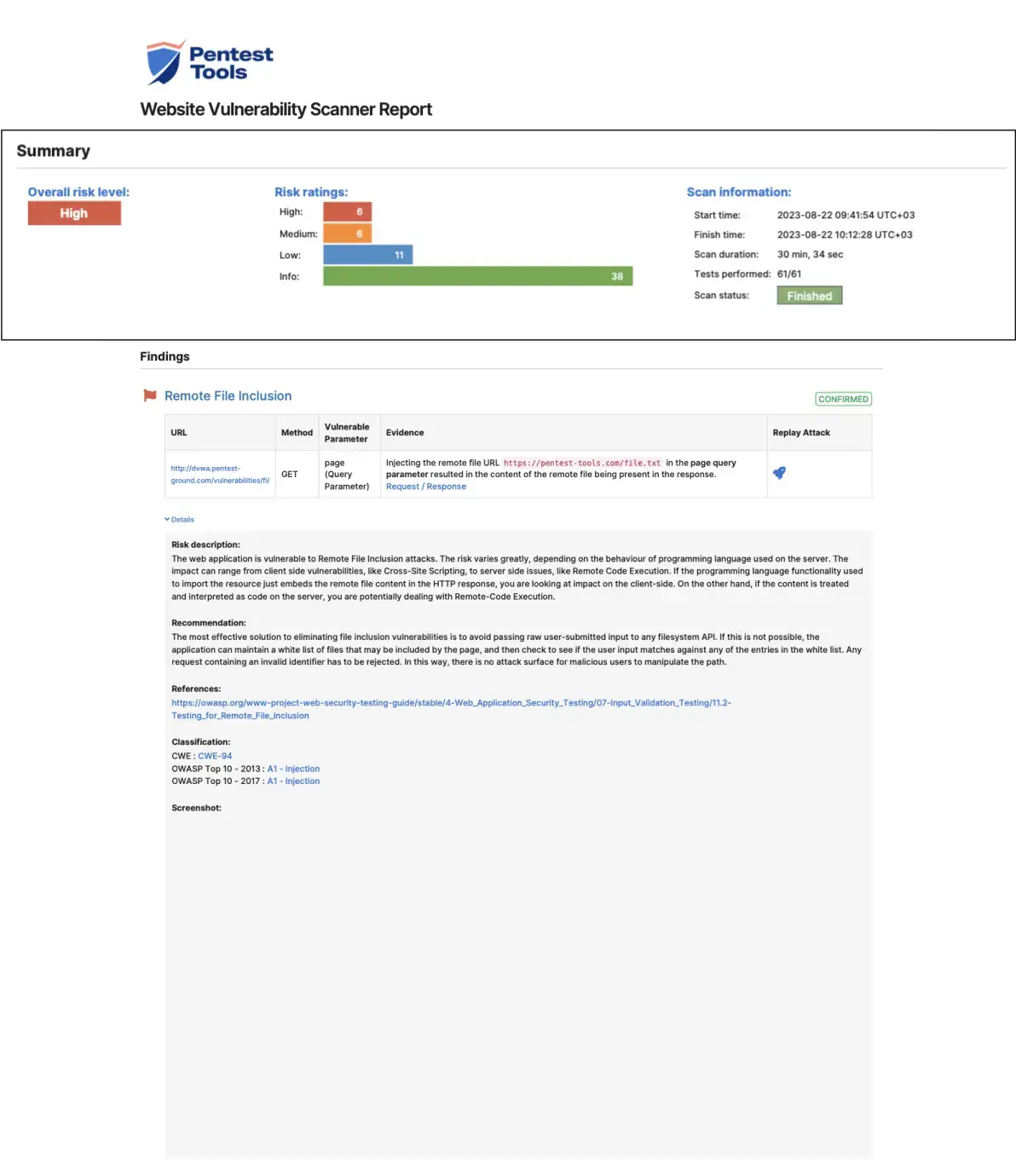
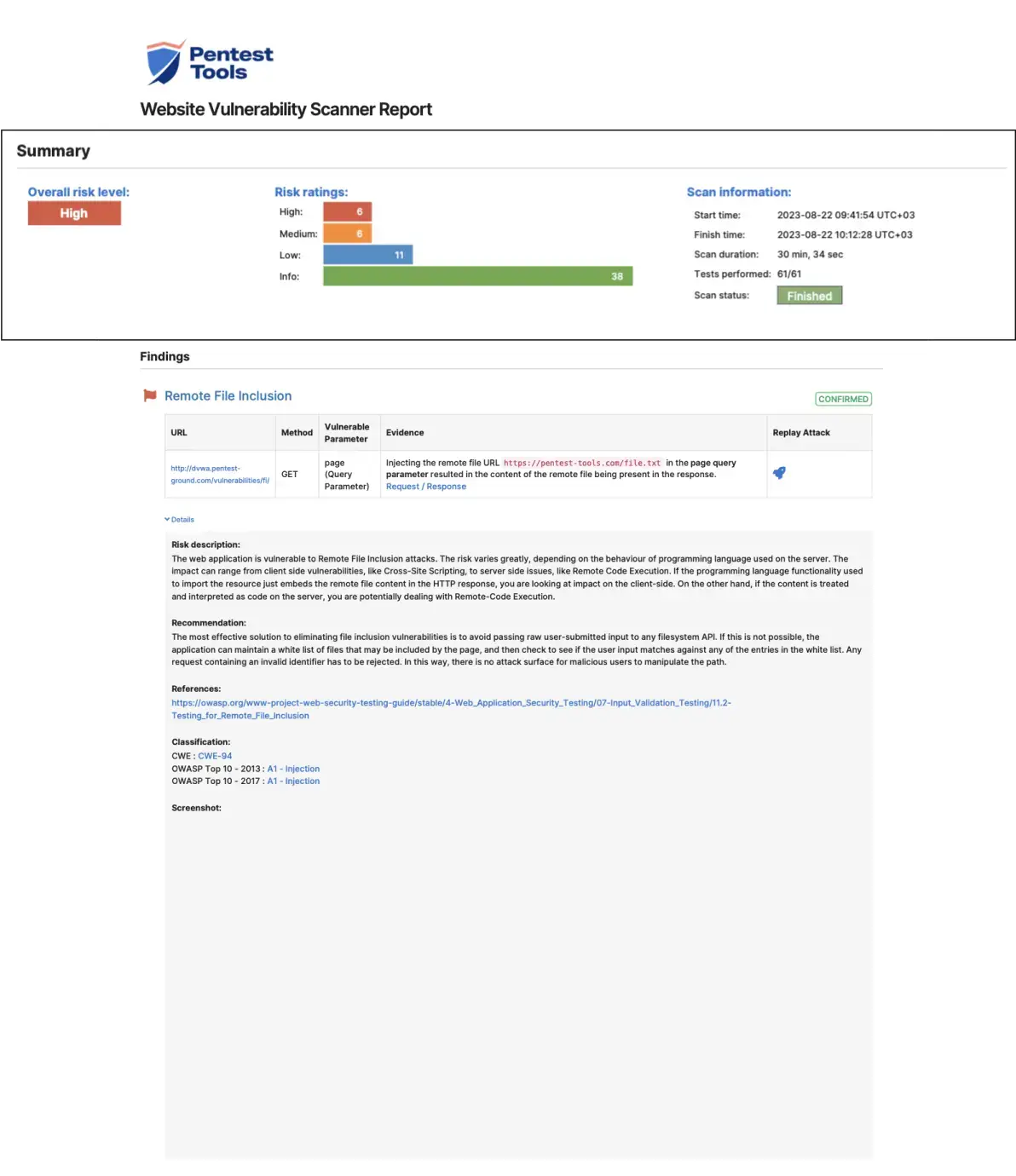
Sample Website Vulnerability Scanner report
This sample report from our scanner shows the main sections it includes, the look and feel, plus the level of detail for the findings.
This section provides a helpful overview of the findings and a visual representation of risk levels across all identified vulnerabilities.
How does the Website Vulnerability Scanner work?
The Website Vulnerability Scanner is a DAST (Dynamic Application Security Testing) tool designed to discover vulnerabilities like XSS, SQL injection, HTTP Prototype Pollution, Directory Traversal, and 75+ more vulnerabilities in running web applications.
The scanner interacts with the target application by sending numerous HTTP requests with specific payloads. If the application is vulnerable, these payloads will determine the code to behave abnormally, informing the scanner that a vulnerability exists.
Cut web fuzzing false positives by 50% with the integrated Machine Learning Classifier
The ML Classifier, a purpose-engineered model integrated into our Website Scanner and URL Fuzzer, helps you filter out noise and zero in on real issues - automatically.
Instead of relying on brittle RegEx logic, the ML Classifier analyzes every HTML response during a scan and every HTML response and assigns it to one of four smart categories:
- HIT: High-value targets like login pages, backups, and exposed secrets
- MISS: Confirmed dead ends, even with misleading status codes
- PARTIAL HIT: Ambiguous but interesting responses, like firewalls
- INCONCLUSIVE: Pages needing browser rendering to confirm
This structured triage filters out dead ends, repeated templates, and language-specific error pages that traditional scanners often mistake for vulnerabilities.
Use this tool from your command line interface
If you prefer it, we also provide a CLI version of our Website Vulnerability Scanner. Through the Pentest-Tools.com CLI, you can run Light scans against your web apps and start gathering insights for your next move.
1. Installation
curl -s https://pentest-tools.com/cli-scan/linux/ptt.zip -o /tmp/ptt.zip
unzip /tmp/ptt.zip -d /tmp/ptt
chmod +x /tmp/ptt/main
sudo mv /tmp/ptt/main /usr/local/bin/pttIf you have docker or pip installed, you can use them to get ptt-scan:
docker run --rm -it pentesttoolscom/ptt-scan:latest run website_scanner https://pentest-ground.com:81/2. Usage
Quickstart: Run the following command in your terminal/command line to find the vulnerabilities of your website.
ptt run website_scanner <target_url>You can learn more options with the -h flag:
ptt -h1. Installation
curl -s https://pentest-tools.com/cli-scan/linux/ptt.zip -o /tmp/ptt.zip unzip /tmp/ptt.zip -d /tmp/ptt chmod +x /tmp/ptt/main sudo mv /tmp/ptt/main /usr/local/bin/pttIf you have docker or pip installed, you can use them to get ptt-scan:
docker run --rm -it pentesttoolscom/ptt-scan:latest run website_scanner https://pentest-ground.com:81/2. Usage
Quickstart: Run the following command in your terminal/command line to find the vulnerabilities of your website.
ptt run website_scanner <target_url>You can learn more options with the -h flag:
ptt -h
Easy enough for quick scans. Advanced enough for deep testing.

Start scanning in seconds - no setup required
As a cloud-based scanner, the Website Vulnerability Scanner on Pentest-Tools.com works out of the box - no installation, configurations, or maintenance needed. Just create an account, enter your target URL, and launch a scan with a preconfigured scan setup - or choose the passive and active checks you need.
Automate website security scans with flexible scheduling
New vulnerabilities love to pop up at the worst times - Friday nights, weekends, you name it. Stay ahead with scheduled scans on your terms - daily, weekly, or whenever you need. The moment our scanner finds a new exposure, it alerts you instantly via email, webhooks, or security tools, so you can strike before attackers do.
Integrate, automate, and streamline with our API
Many security teams prefer to trigger scans programmatically using our REST API. This enables quick integration with CI/CD pipelines, security dashboards, vulnerability management tools, or custom applications - eliminating repetitive, time-consuming work and making security testing an integral part of your development process.
Scan internal web apps without making assets public
Need to scan apps behind firewalls, on private clouds, or internal networks? Our VPN Agent securely routes traffic from our cloud-based scanner to your internal infrastructure - so you can detect risks without exposing your assets to the internet.
Integrate scans results into the tools you already use
Keep vulnerabilities out of spreadsheets and in the tools that matter. Sync findings with Jira, Slack, CI/CD pipelines, GitHub Actions, Microsoft Teams, and Vanta. Need more control? Use webhooks or the Pentest-Tools.com API to push security issues into your custom dashboards.
Customer reviews
Pentest-Tools.com is my team's first go-to solution. Anytime we are preparing to deploy a new version of our software, we run many tools to monitor and secure our environment, but the simplicity and ease we have with Pentest-Tools.com to run network and web server scans to highlight issues is unmatched.
Michael Dornan
CEO at Tili Group
Israel 🇮🇱


Common questions about web vulnerability scanning
A web vulnerability scanner is a specialized software tool designed to automatically identify security flaws within web applications. A reliable, robust website security scanner should be able to mimic real attacker tactics and identify realistic, exploitable security issues.
Our Website Vulnerability Scanner is a robust example of this type of tool, offering a comprehensive scan that identifies threats and also validates them to reduce false positives.
It works by interacting with the target application, sending a series of HTTP requests with specific payloads, and analyzing the responses to detect potential vulnerabilities such as Cross-Site Scripting (XSS), SQL injection, OWASP Top10, and other pressing security issues and misconfigurations.