Free cPanel vulnerability scanner - detect CVE-2026-41940
This free cPanel vulnerability scanner checks if your target is affected by CVE-2026-41940 - a critical (CVSS 9.8) authentication bypass in cPanel and WHM.
Active exploitation is confirmed in the wild for this CVE that lets unauthenticated attackers gain full administrative access remotely.
With approximately 1.5 million cPanel instances directly exposed to the internet, any unpatched server is a target. See the technical details and mitigation steps below.
This scan can take up to 2 minutes after which you'll get a PDF report you can share with your team.
- Scan type
Light scan
Want to detect over 16,000 vulnerabilities across your infrastructure? This free tool is part of the Network Vulnerability Scanner included in all our pricing plans.
This free cPanel vulnerability scanner checks if your target is affected by CVE-2026-41940 - a critical (CVSS 9.8) authentication bypass in cPanel and WHM.
Active exploitation is confirmed in the wild for this CVE that lets unauthenticated attackers gain full administrative access remotely.
With approximately 1.5 million cPanel instances directly exposed to the internet, any unpatched server is a target. See the technical details and mitigation steps below.
This scan can take up to 2 minutes after which you'll get a PDF report you can share with your team.
What is CVE-2026-41940 (cPanel & WHM authentication bypass)?
Technical details
CVE-2026-41940 is a critical authentication bypass vulnerability affecting cPanel & WHM and WP Squared, disclosed on April 28, 2026. The root cause is a CRLF injection flaw in the way cPanel reads and writes session files.
Specifically, cpsrvd - the cPanel service daemon - writes a new session file to disk before authentication completes. An attacker can manipulate the whostmgrsession cookie by omitting an expected segment of the cookie value, causing cpsrvd to bypass the normal encryption process when writing the session file. By injecting \r\n sequences into user-controlled input that ends up in that file, the attacker inserts arbitrary key-value pairs - including authentication state flags - before the session is ever validated.
The result: an unauthenticated attacker can craft a request that, when processed by cPanel, writes a session file containing cp_auth=1 (or an equivalent authentication flag). On the attacker's next request, cPanel reads back the tampered session file and treats the session as authenticated - granting full access to the cPanel or WHM interface without ever supplying valid credentials.
cPanel is one of the most widely deployed web hosting control panels in the world, running across hosting environments that serve enterprises, government agencies, banks, and hundreds of thousands of smaller organizations globally. A single cPanel server typically hosts dozens to hundreds of separate customer sites - meaning a successful unauthenticated authentication bypass doesn't just affect one target, it potentially exposes every account on that server.
That's what makes CVE-2026-41940 unusually high-stakes: the vulnerability is in the infrastructure that underlies a large portion of the hosted web itself.
How we detect CVE-2026-41940
Our Network Vulnerability Scanner sends multiple crafted requests to the target's cPanel login endpoint, injecting CRLF sequences into session-related parameters.
Detection is confirmed through multiple tactics, not inferred from version banners alone. The scanner validates exploitability by observing the server's actual response to the crafted payload.
Products affected by CVE-2026-41940
This vulnerability affects cPanel & WHM and WP Squared. Both the cPanel (user-facing) and WHM (host-facing) interfaces are impacted, since they share the underlying session-handling code.
Affected components include:
- cPanel user interface (port 2082 / 2083)
- WHM administrator interface (port 2086 / 2087)
- cPanel XML-API and UAPI endpoints that rely on session authentication
- WP Squared (WordPress hosting platform built on cPanel)
The following cPanel & WHM versions are vulnerable (all versions prior to the patched releases listed below):
| Branch | First patched version |
|---|---|
| 11.110.x | 11.110.0.97 |
| 11.118.x | 11.118.0.63 |
| 11.126.x | 11.126.0.54 |
| 11.132.x | 11.132.0.29 |
| 11.134.x | 11.134.0.20 |
| 11.136.x | 11.136.0.5 |
Source: NVD / VulnCheck advisory, April 29, 2026..
CVE-2026-41940 severity
CVE-2026-41940 carries a critical severity rating of 9.8.
Given exploitation requires no authentication, no user interaction, and no special privileges, a CVSSv3 base score in the 9.x–10.0 range is expected.
How attackers can exploit CVE-2026-41940
This vulnerability is straightforward to exploit remotely:
- No credentials required - unauthenticated exploitation.
- No user interaction required - the attacker does not need to trick anyone into clicking a link.
- Remotely exploitable - any internet-exposed cPanel or WHM instance is at risk.
- Public PoC available - watchTowr and Searchlight Cyber published a detailed proof-of-concept alongside their disclosure.
The real-world impact of a successful exploit is severe.
Once authenticated to cPanel, an attacker can:
- read and modify all files hosted on the account
- access databases
- steal stored credentials
- deploy webshells or malware
- escalate to WebHost Manager (root-level) access via privilege escalation chains
- pivot to other hosted sites on the same server
CVE-2026-41940 disclosure timeline
| Date | Events |
|---|---|
| April 28, 2026 | CVE-2026-41940 is publicly disclosed. watchTowr publishes a detailed analysis and proof-of-concept on their blog, including the CRLF injection mechanism and the session-file parsing flaw. |
| April 28, 2026 | cPanel & WHM releases patches. Administrators are strongly urged to update immediately. |
| April 30, 2026 | Detection of CVE-2026-41940 is added to the Network Vulnerability Scanner on Pentest-Tools.com. |
How to mitigate CVE-2026-41940
The primary remediation is to update cPanel & WHM to a patched version immediately. Vendor advisories are available for cPanel & WHM and WP Squared. Given that active exploitation is confirmed and a public PoC exists, treat this as an emergency patch.
If you cannot update immediately, apply these mitigating controls - but understand they are not fixes:
- Restrict access to cPanel and WHM interfaces (ports 2082, 2083, 2086, 2087) to trusted IP ranges using firewall rules or cPanel's Host Access Control.
- Disable external access to the WHM interface if it is not required by your operations.
- If your infrastructure sits behind Cloudflare, verify that the Cloudflare Managed Ruleset is enabled - an emergency WAF rule blocking CVE-2026-41940 exploitation attempts was deployed on April 30, 2026. This is a partial control, not a substitute for patching.
- Monitor cPanel access logs for unexpected authenticated sessions, especially from unfamiliar IPs or with unusually short authentication times.
- Enable cPHulk Brute Force Protection, which may partially limit some exploitation patterns.
Note: IP restrictions, WAF rules, and logging are mitigating controls. The only reliable remediation is applying the vendor patch.
CVE-2026-41940 references
- Pentest-Tools.com Vulnerability & Exploit Database - CVE-2026-41940
- cPanel & WHM vendor security advisory (April 28, 2026)
- watchTowr Labs - technical analysis and PoC
- Searchlight Cyber - technical analysis and PoC
- NVD - CVE-2026-41940
- Cloudflare emergency WAF rule - April 30, 2026
- WP Squared vendor advisory
CVE-2026-41940 scanner report
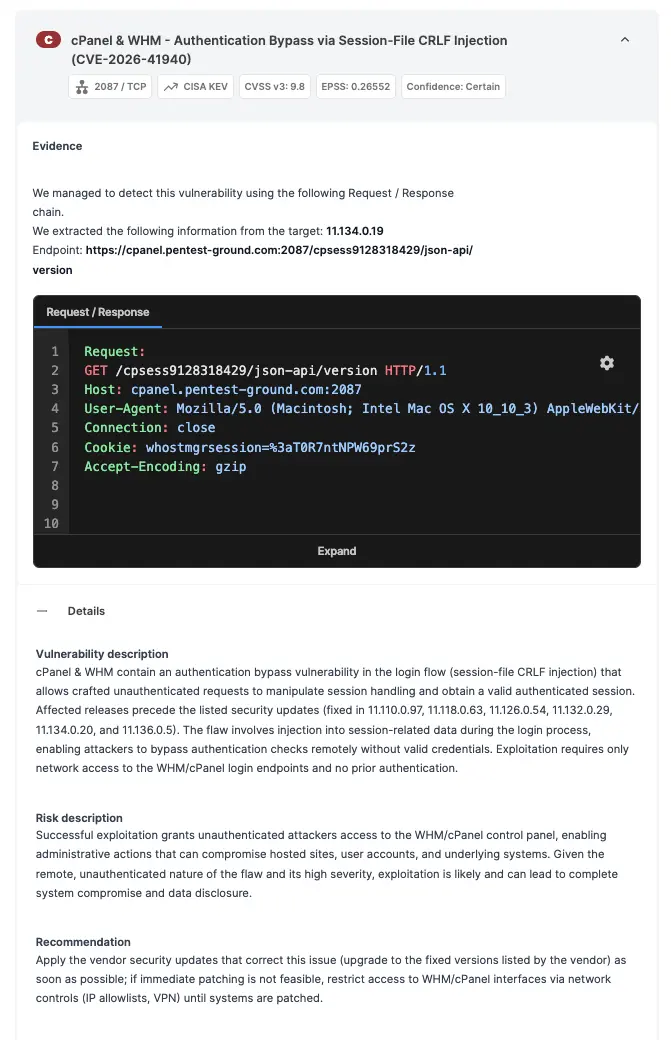
Once the scan completes, you'll get a finding report you can export as PDF.
Here's what a positive detection looks like - including the evidence, risk context, and remediation guidance you can share with your team or clients:
About our Network Vulnerability Scanner
Our Network Vulnerability Scanner is a well-rounded tool for all your network security assessments.
It combines multiple engines and fine-tuned (customizable) scan settings which surface almost 17,000 vulnerabilities, misconfigurations, and outdated services.
Each scan automatically updates your attack surface and provides an up-to-date map for planning targeted attacks or strategic lateral movements.
Explore a sample report which includes a vulnerability summary, automatically confirmed findings, evidence, and more.
See what else it can doIn a transparent benchmark, our tool outperformed the 6 most popular network scanners on the market - both open-source and commercial.
FAQs
What are cPanel and WHM (WebHost Manager)?
cPanel and WHM (WebHost Manager) is one of the world's most widely deployed web hosting control panels. cPanel provides the user-facing interface for managing websites, email accounts, databases, and files.
WHM provides the administrator interface for managing the server and creating or administering cPanel accounts. Because of its ubiquity in shared, VPS, and dedicated hosting environments, cPanel is an extremely high-value target: compromising one cPanel instance can expose hundreds of hosted websites on the same server.
What is CRLF injection?
CRLF stands for carriage return (\r, ASCII 0x0D) and line feed (\n, ASCII 0x0A). These characters are used as line delimiters in many text-based protocols and file formats. A CRLF injection vulnerability occurs when an application accepts user-controlled input and writes it to a file or HTTP response without properly stripping or encoding these characters.
An attacker who can inject \r\n sequences can insert new lines - and therefore new structured data - into the output, potentially manipulating how the application interprets that data. In the case of CVE-2026-41940, the injected lines manipulate cPanel's session files to set authentication flags that grant unauthorized access.
How widespread is the CVE-2026-41940 exposure?
Approximately 1.5 million cPanel and WHM interfaces are directly exposed to the internet, based on Shodan data. Any unpatched instance is potentially exploitable by any unauthenticated remote attacker - no credentials, no prior access, no user interaction needed.
The risk is compounded by cPanel's role in the web hosting ecosystem. Because one cPanel server hosts many sites and customers, a single successful exploit affects everyone on that server - not just the primary account holder.
This makes CVE-2026-41940 a high-priority issue for hosting providers, managed service providers, and any organization that runs cPanel infrastructure for multiple clients.
Why are you offering a free scanner for CVE-2026-41940?
Every day, our team develops tools, detections, and exploits to help security professionals find vulnerabilities before attackers can exploit them.
We know the fight is unfair: security teams follow strict rules, while threat actors do whatever they want. That's why we build free tools like this one - so security teams can validate their exposure quickly, without waiting for a scheduled scan or a costly engagement.
Does the Cloudflare WAF protect against CVE-2026-41940?
Cloudflare deployed an emergency WAF rule on April 30, 2026, blocking exploitation attempts that match the known CVE-2026-41940 attack pattern. If your infrastructure sits behind Cloudflare and the Cloudflare Managed Ruleset is enabled, you have a layer of network-level protection.
However, WAF rules are not a substitute for patching. A WAF inspects traffic at the network edge - it cannot address the underlying flaw in cPanel's session-handling code. Attackers may find bypass techniques that evade WAF signatures. Applying the cPanel vendor patch is the only complete remediation.
